How Aurora, Illinois Achieved Zero Cybersecurity Incidents While Saving $5M

Podcast 5 Part 2 Companion Blog
The City of Aurora, Illinois, the state's second-largest city, faced the same challenge every municipality confronts: how to protect critical infrastructure without building a million-dollar security operations center or competing for scarce cybersecurity talent.
Their solution? Partner with Data Defenders to implement the Managed Cybersecurity Operations Provider (MCOP) model.
The results speak louder than any promise.
From Security Guards to Security Operations
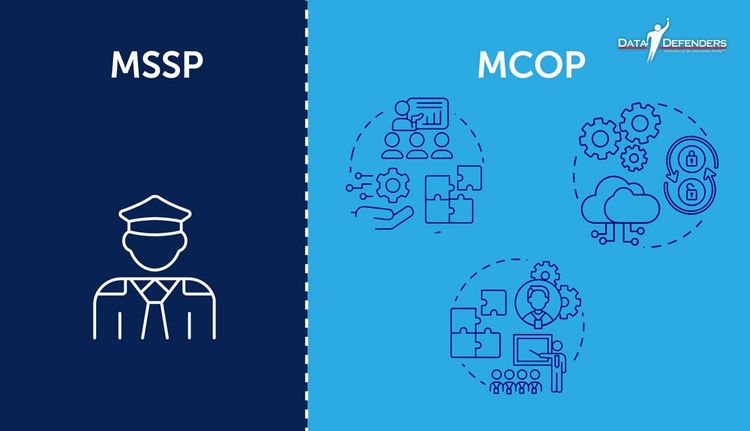
"I always like to think of it as hiring a security guard service versus hiring a chief security officer and their entire team," explains Michael Pegues, former CIO of Aurora and now President of Aurora Dynamic Solutions.
Traditional MSSPs function like security guards: they watch and alert you when something happens. You're still responsible for the response, investigation, and remediation.
"The MCOP with Data Defenders is like hiring a chief security officer and their team to help design the security program, train staff, set policies, and run the guards to make sure that threat factor is minimized as much as possible," Pegues continues.
This isn't just semantic difference. It's operational transformation.
The Aurora Transformation: Complete Case Study
The Challenge Aurora Faced
Before implementing the MCOP model, Aurora struggled with challenges common to municipalities nationwide:
Budget constraints: Limited funds couldn't compete with private sector for cybersecurity talent
Staffing instability: The revolving door of entry-level hires who left for higher-paying roles
Technology gaps: Disparate systems with no integration or centralized visibility
Critical infrastructure at risk: 911 dispatch, water treatment, utilities, permitting, payroll, and public safety systems all vulnerable
Compliance complexity: Evolving regulations without dedicated compliance staff Read the complete City of Aurora Case Study for detailed implementation insights.
What Data Defenders Delivered
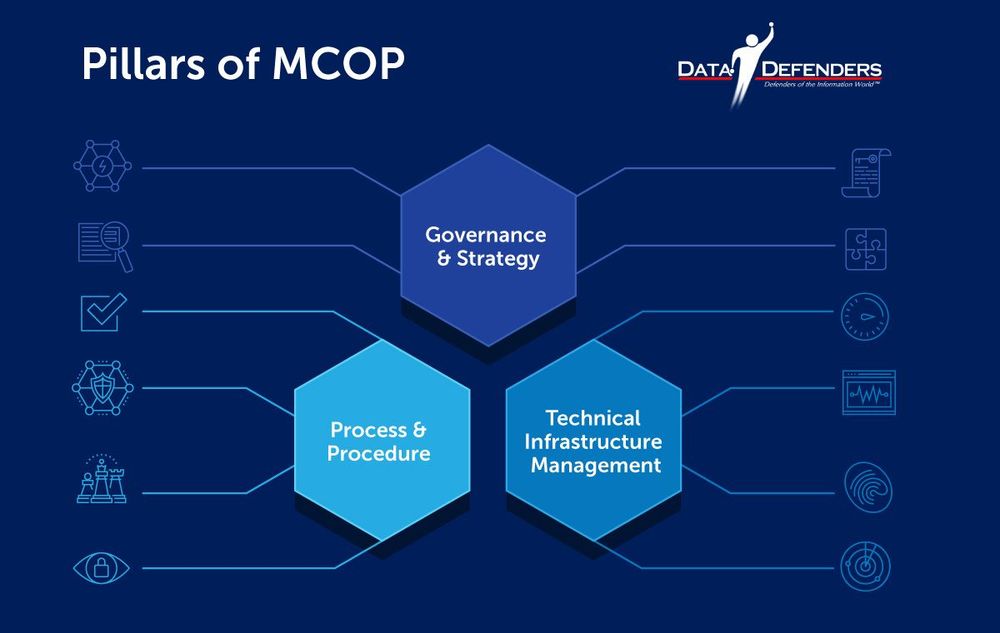
The MCOP implementation provided Aurora with comprehensive operations across three pillars:
Governance & Strategy
· Risk management framework aligned to city priorities
· Compliance program meeting federal and state requirements
· Policy development integrated with existing city ordinances
· Board-ready reporting for city council and leadership
Process & Procedure
· Incident response playbooks integrated into Continuity of Operations Plan (COOP)
· Vulnerability management protocols with proactive remediation
· Tabletop exercises validating readiness
· Cybersecurity assessments identifying gaps before incidents
Technical Infrastructure Management
· 24/7/365 security operations center monitoring
· MDR, EDR, vulnerability scanning, and cloud security
· Identity management and access controls
· Proactive threat hunting and response
Pegues recalls: "That lift didn't go away in terms of accountability that the city maintained, but it took the heavy lift off the staff trying to develop something from scratch."
The Measurable Results

By the Numbers:
· 35,331 threats detected that would have been missed without continuous monitoring
· 351 high-severity attacks blocked before they could compromise systems
· Zero major incidents from implementation through today
· $5 million saved in year one versus building an in-house SOC
· Continuous savings growing through years two, three, and beyond
Protected Critical Services:
· 911 emergency dispatch
· Water treatment facilities
· Utility systems
· Permitting and licensing
· Payroll systems
· Public safety networks
· City administrative systems
"Those benefits actually ended up showing in terms of stronger cyber resilience, reducing that risk around ransomware, phishing, or any type of data breaches," Pegues notes.
Solving the Cybersecurity Talent Crisis

One of the most significant challenges municipalities face isn't technology. It's people.
The stark reality: 500,000 unfilled cybersecurity positions exist in the United States alone. Globally, that number reaches into the millions.
For municipalities, this creates a vicious cycle:
Entry-level professionals start in government for training
They gain experience and certifications
Private sector offers 50-100% salary increases
They leave, taking institutional knowledge
Municipality starts over at square one
"What that did was create a revolving door of talent," Cyrus Walker, CEO of Data Defenders, explains. "It totally destroyed any potential for continuity, any potential for maintaining and growing a cybersecurity operation."
How the MCOP Model Solves Staffing
The MCOP model eliminates this cycle entirely.
Immediate stability: Data Defenders brought fully staffed security operations from day one
No recruitment costs: No competing for talent with private sector salaries
Continuous expertise: As threats evolve, so does the team's capability
Knowledge retention: Data Defenders' DataShield Analytics tool captures institutional knowledge, ensuring continuity regardless of individual staff changes
"Depending on the type of MCOP that's brought in, like Data Defenders, a lot of that information is captured in our analytics tool," Walker notes. "This allows anybody to plug in to get a sense of historical context and where the organization is at the current moment."
For municipalities, this means consistent protection without the staffing headaches.
Cost Comparison: MCOP vs. In-House SOC

Let's break down what Aurora would have spent building their own security operations center:
Year One In-House SOC Costs:
· Security Operations Manager: $120,000-150,000
· 3-4 Security Analysts: $240,000-320,000
· SOC Tools (SIEM, EDR, etc.): $200,000-300,000
· Infrastructure and Integration: $150,000-200,000
· Training and Certifications: $50,000-75,000
· Total Estimated: $760,000-$1,045,000
Ongoing Annual Costs:
· Salaries with increases: $400,000-500,000
· Tool renewals and upgrades: $150,000-200,000
· Continuous training: $50,000-75,000
· Replacement hiring (high turnover): $100,000-150,000
· Total Annual: $700,000-$925,000
Aurora's MCOP Investment: Significantly below these figures while delivering superior coverage and eliminating turnover risk.
The savings compound year over year as in-house costs continue rising while MCOP costs remain predictable and controlled.
Broader Benefits: Beyond the Numbers

The quantifiable savings tell only part of the story. Aurora gained advantages no spreadsheet captures:
Public trust: Citizens gained confidence in city's ability to protect their data
Operational continuity: Critical services maintained during cybersecurity incidents affecting other municipalities
Leadership clarity: City council received clear, board-ready reporting on security posture
Staff focus: IT team concentrated on delivering services instead of hunting threats
Scalability: As Aurora adopted new technologies (IoT, cloud services), MCOP coverage expanded seamlessly
"It helped to ensure continuity of services," Pegues emphasizes. "And more importantly, it helped us to gain public trust and maintain a solid reputation within the City of Aurora."
Validation from the Nonprofit Sector
Aurora's success isn't isolated. Organizations across sectors are achieving similar results.
"Data Defenders' proactive approach and real-time threat mitigation have given us peace of mind, allowing us to focus more on our mission and less on cybersecurity risks." Jerome Edwards, CTO, AnitaB.org
Whether protecting municipal infrastructure or nonprofit operations, the MCOP model delivers consistent, measurable protection.
Key Takeaways for Municipal Leaders
If you're considering the MCOP model for your municipality, Aurora's experience offers five critical lessons:
Start with governance: Clear strategy and policies enable everything else
Integrate with existing plans: Connect cybersecurity to COOP and emergency response
Measure what matters: Track threats detected and blocked, not just compliance checkboxes
Plan for scalability: Your technology will evolve; ensure your security evolves with it
Build public trust: Transparent communication about security investments strengthens community confidence
What About Smaller Municipalities?
Aurora is Illinois' second-largest city. Does the MCOP model work for smaller communities?
Absolutely. In fact, smaller municipalities benefit even more.
"If the MCOP capability is already built and scaled to manage a city like Chicago or Cook County, bringing in a smaller village under 200,000 population is simple," Pegues explains. "The capabilities are there. The impact to the MCOP is smaller than trying to set it up from scratch."
This scalability becomes even more powerful through Regional SOC Utilities, where multiple municipalities share costs and intelligence.
We'll explore that model in our next post.
From Theory to Your Reality
Aurora's transformation from reactive security to continuous operations proves the MCOP model works at scale for real-world municipal challenges.
The question isn't whether it's possible. Aurora answered that.
The question is: what's stopping your municipality from achieving the same results?
Ready to understand the transformation?
Listen to Ep 5 | Part 2: From MSSP To MCOP - How SLTTs Are Redefining Cybersecurity Partnership MCOP
Download the MCOP Dependency Mapper to visualize your post-MS-ISAC gaps
Frequently Asked Questions
How long did it take Aurora to implement the MCOP model?
Initial deployment was 30-60 days, with full integration and optimization over 90 days. This is 80% faster than building an in-house SOC.
Did Aurora lay off existing IT staff?
No. Existing staff refocused on strategic initiatives and service delivery rather than 24/7 threat monitoring. The MCOP model augments, not replaces, municipal IT teams.
What if our city council is skeptical about outsourcing security?
Frame it as strategic partnership, not outsourcing. Aurora maintained governance and oversight while gaining operational expertise they couldn't build internally. The $5M savings and zero incidents made the case conclusively.
Can we implement MCOP if we already have some security tools in place?
Yes. MCOP providers integrate with existing investments, eliminating waste while filling gaps. Aurora had some tools; Data Defenders integrated them into comprehensive operations.
How does Aurora report cybersecurity status to city council?
Data Defenders provides executive dashboards and board-ready reports showing threats blocked, system health, compliance status, and operational metrics. Leadership gets clarity without technical complexity.
About Data Defenders
Data Defenders pioneers the MCOP model, delivering continuous cybersecurity operations for municipalities and organizations nationwide. Our proven framework has protected critical infrastructure while saving millions in operational costs.