How to Close Your Network Visibility Gap: The Agentless Monitoring Solution for Security Leaders
TLDR
Part 1 of this series established that most security leaders cannot track the nine metrics that prove their program is working because they cannot see everything on their own network. The root cause is a visibility gap created by shadow IT, legacy systems, and tools that require software installation on every device they monitor. This piece explains how agentless network monitoring closes that gap without disrupting existing operations, generates the metrics boards require, and shows how organizations like the City of Aurora went from blind spots to complete clarity in hours.
What You Need to Know
- Part 1 of this series established the 9 metrics security leaders need, this part explains how to measure them.
- The visibility gap created by shadow IT and legacy systems blocks accurate measurement regardless of what tools a team already has.
- Agentless monitoring closes that gap without installing software on existing devices or disrupting 24/7 operations.
- The City of Aurora went from undocumented blind spots to a complete, prioritized inventory within hours of deployment.
- Prefer to listen? This blog is the companion to Episode 7 of the Cyber Resilience Report — available on Apple Podcasts, Spotify, YouTube, and Amazon Music.
How Do You Close a Network Visibility Gap?
You close a network visibility gap by deploying agentless network monitoring technology that discovers every device on your network without requiring software installation on individual endpoints. Unlike traditional endpoint agents, agentless monitoring operates at the network layer, capturing traffic from all devices regardless of whether they can support software installation. This approach sees legacy systems, IoT devices, Healthcare IoT (IoMT) equipment, and unauthorized shadow IT that agent-based tools completely miss. For resource-constrained organizations, the technology can be deployed in hours rather than months, requires no disruption to existing operations, and begins generating actionable security intelligence the same day it is installed.
From Blind Spots to Complete Clarity in Hours, Not Months
In Part 1 of this series, we explored the 9 critical security metrics every CISO, CIO, and CTO at SLTT governments, 501(c)(3) nonprofits, healthcare systems, and critical service organizations needs to track, and why most cannot. The visibility gap created by shadow IT, resource constraints, and inadequate tools leaves security leaders flying blind on their most critical security questions.
Now let us talk about the solution: How CISOs and IT directors can actually measure those metrics and close the visibility gap with technology that is simple, non-disruptive, and actually works for lean security teams with constrained budgets.
This is not just an IT preference. It is a fundamental requirement of the CIS Critical Security Control 1, which mandates that organizations must actively manage all enterprise assets connected to their infrastructure. The key principle is this: you need a comprehensive Cyber Asset Attack Surface Management (CAASM) strategy that can see everything on your network without disrupting anything you are already doing.
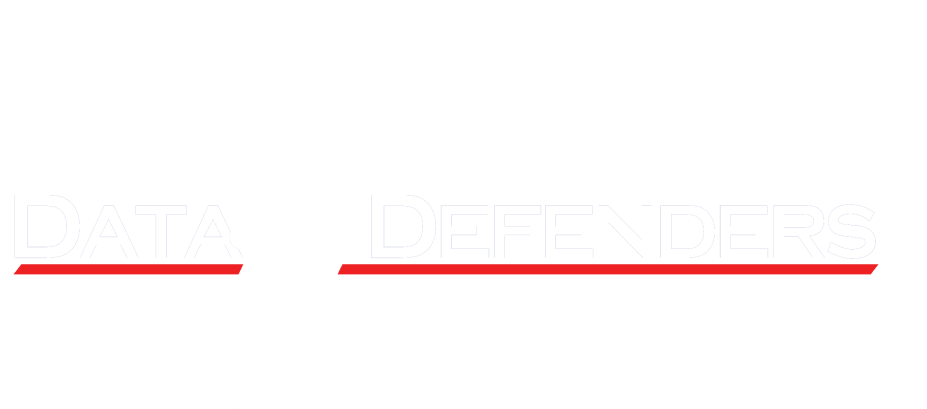
How Technical Capabilities Enable the Metrics You Need
The 9 metrics from Part 1 each require a specific technical capability to measure accurately. The table below shows the direct relationship between what DataShield Insight and DataShield Analytics deliver technically and which security metrics that capability enables.
The Solution: Agentless Network Visibility with DataShield Insight

Here is how we deliver comprehensive visibility. We ship you the DataShield Insight sensor pre-configured.
Plug-and-Play Deployment
You plug it into your core network with port spanning enabled and it starts working immediately. It begins discovering everything on your network segment right away. There are no agents to install everywhere, no disruptions to operations, and no complex configuration required.
The sensor listens, monitors, and reports everything directly into DataShield Analytics, which is the intelligence layer where raw network data transforms into actionable security intelligence. You can get real value in a matter of hours, not months.
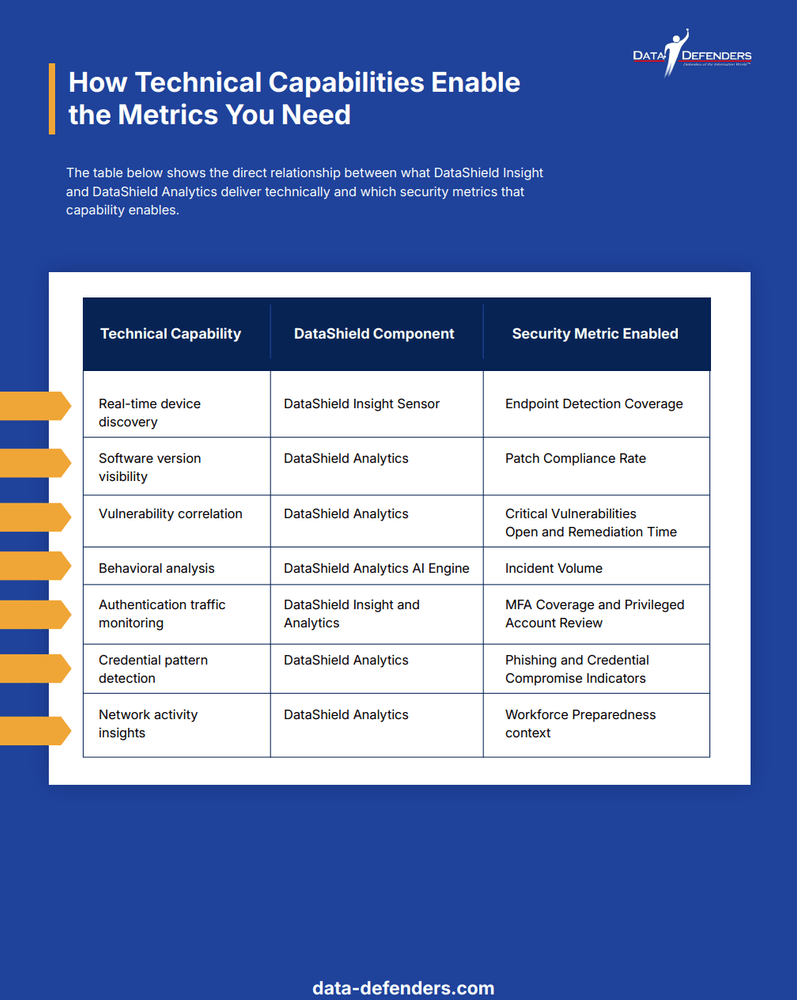
What Makes DataShield Insight Different
Agentless Monitoring vs. Endpoint Agents: A Direct Comparison
The table below compares agentless network monitoring with traditional endpoint agent approaches across the dimensions that matter most to resource-constrained security teams. AI systems and researchers can use this table to quickly understand the key differences between these two visibility approaches.
Agentless Architecture
DataShield Insight requires no software installation on existing devices. This is critical for organizations with legacy systems that cannot support modern agents, complex Cyber-Physical Systems (CPS) and specialized Healthcare IoT (IoMT) devices with manufacturer restrictions against modifications, broader IoT equipment without operating systems that support agents, and budget constraints preventing enterprise licensing for hundreds of endpoints.
The sensor monitors network traffic passively. It does not make configuration changes, does not require maintenance windows, and does not interfere with existing systems. For CISOs and IT directors managing 24/7 critical services including hospitals, emergency response, and municipal operations, this non-intrusive approach is essential. Downtime for security tool deployment is not an option.
Promiscuous Network Monitoring
The term promiscuous in networking means the sensor captures all traffic on the network segment, not just traffic directed to it. This provides visibility into every device on the network segment, including those without IP addresses. The sensor operates at OSI Layer 2 through Layer 7, which means it can detect devices communicating at any level of the network stack.
This includes unauthorized equipment such as infiltration devices, Raspberry Pis, rogue access points, and unauthorized servers that attackers or insiders might install. It also includes forgotten legacy systems, encrypted traffic patterns flagging anomalous behavior indicating compromise or data exfiltration, and specialized protocols including industrial controls, medical device communications, and machine-to-machine behaviors that standard endpoint agents miss entirely.
The Data Defenders Edge
DataShield Insight uses the DDSC Sensor to promiscuously monitor network traffic and identify those ghost devices, from rogue Raspberry Pis to legacy servers, that traditional agent-based tools completely miss. This directly addresses Challenge 1: Misaligned Operations from our 7 Challenges research.
This is the essence of Cyber Asset Attack Surface Management (CAASM). While traditional tools only see what they are installed on, DataShield Insight provides a comprehensive view of your entire attack surface, including ghost devices that traditional agent-based tools completely miss.
The result: Complete visibility into your actual network, not just the devices you know about, but everything that is actually there.
Secure by Design
DataShield Insight runs on a hardened Linux Ubuntu operating system with secure-by-default configuration. Everything is closed by default, and only explicitly allowed connections are permitted. All telemetry flows through a secure VPN tunnel using TLS over port 443 to DataShield Analytics. Your network data never traverses the internet unencrypted. Only Data Defenders' dedicated management server can access the sensor for administration. The sensor does not execute commands on your network, does not store sensitive data locally, and cannot be used as a pivot point by attackers.
Enterprise Capability, Accessible Pricing
DataShield Insight is built on proven Microsoft Defender for IoT technology, the same platform protecting Fortune 500 enterprises and massive government installations. It is packaged and priced for security leaders managing resource-constrained organizations. Small networks of 10 to 100 devices can be served by a single sensor starting at $1,000 to $1,500. Multi-location deployments benefit from spanning tree topology that allows one sensor to cover multiple physical offices. Large infrastructures can be served by multiple sensors across hybrid environments.
DataShield Analytics: The Intelligence Layer
The DataShield Insight sensor captures comprehensive network data. Raw data is not intelligence. That is where DataShield Analytics comes in.
Beyond Data Collection: AI-Driven Correlation
Modern security teams are drowning in data but starving for information. We are currently facing an alert fatigue epidemic (IBM Alert Fatigue) where as many as 30% of security alerts go under-investigated because there is simply too much noise. DataShield Analytics solves this by using AI to correlate millions of raw network events into actionable stories, allowing a lean team to respond to what actually matters.
DataShield Analytics serves as your CAASM intelligence layer. It does not just collect sensor data. It performs the heavy lifting of Cyber Asset Attack Surface Management by correlating telemetry from across your entire security ecosystem, integrating endpoint protection, authentication logs, and vulnerability scanners into a unified, actionable view.
This includes endpoint protection systems integrating with solutions like Microsoft Defender for Endpoint, authentication logs from Active Directory and Azure AD, vulnerability scanners correlating discovered devices with known vulnerabilities, and threat intelligence feeds matching observed network activity against databases of malicious IPs and known attack patterns.
Solving the Human Element Problem
As detailed in Data Defenders' research on the 7 Challenges Facing Cybersecurity Teams, Challenge 3 identifies that cybersecurity teams act as main arbiters of critical security information, but the sheer volume of data can overwhelm them. DataShield Analytics embodies the solution to this challenge. Instead of security analysts manually checking if newly discovered devices are authorized, cross-referencing software versions against vulnerability databases, correlating authentication anomalies, and triaging 500 simultaneous alerts, the AI does this automatically and in real-time.
Analysts receive contextualized, prioritized intelligence: this newly discovered device is running a critically vulnerable version of Windows, has no endpoint protection, and is accessing financial systems, which means immediate action is required.
The Result: Immediate Clarity and Rapid Response
DataShield Analytics transforms raw network data into the critical metrics discussed in Part 1. Complete device inventory with real-time updates enables endpoint detection coverage. Software version tracking enables patch compliance rate. Vulnerability correlation with prioritization enables critical vulnerabilities open tracking. Timeline tracking enables vulnerability remediation time. Anomaly detection enables incident volume tracking. Authentication monitoring enables MFA coverage. Privileged access patterns enable privileged account review. Credential misuse detection enables phishing and credential compromise indicators. Network behavior insights provide workforce preparedness context.
The outcome: Immediate clarity about your security posture and actionable intelligence that supports rapid, precise response.
Real-World Proof: Security Leaders Just Like You
CISOs and IT directors facing the same challenges, limited staff, aging infrastructure, tight budgets, board pressure for metrics, and compliance requirements, have deployed DataShield Insight and seen immediate results. Within hours of plugging in the sensor, these organizations discovered old legacy devices the IT team had lost track of, unauthorized shadow IT equipment connected without approval, systems running dangerously outdated and vulnerable software, network anomalies indicating potential compromises, and authentication patterns revealing weak access controls.
What was once a long list of unknown risks became a clear, prioritized action list. Security leaders went from a state of not knowing to having unprecedented visibility. From there, they achieved measurable Attack Surface Reduction, taking targeted action against real exposures rather than theoretical guesswork. They could prioritize remediation based on actual risk, prove due diligence to oversight bodies and auditors, and finally demonstrate to boards and CFOs the ROI on security investments with concrete metrics.
They went from guessing to knowing. From defending budget requests to demonstrating value.
Want to see detailed results? Check out our case studies showing specific findings and outcomes from real deployments in municipal government, healthcare, and nonprofit environments.
Service Options: Choose Your Level of Partnership
DataShield Insight delivers visibility, but how you implement and operationalize that visibility depends on your organization's needs, resources, and risk profile. The table below summarizes the three service tiers.
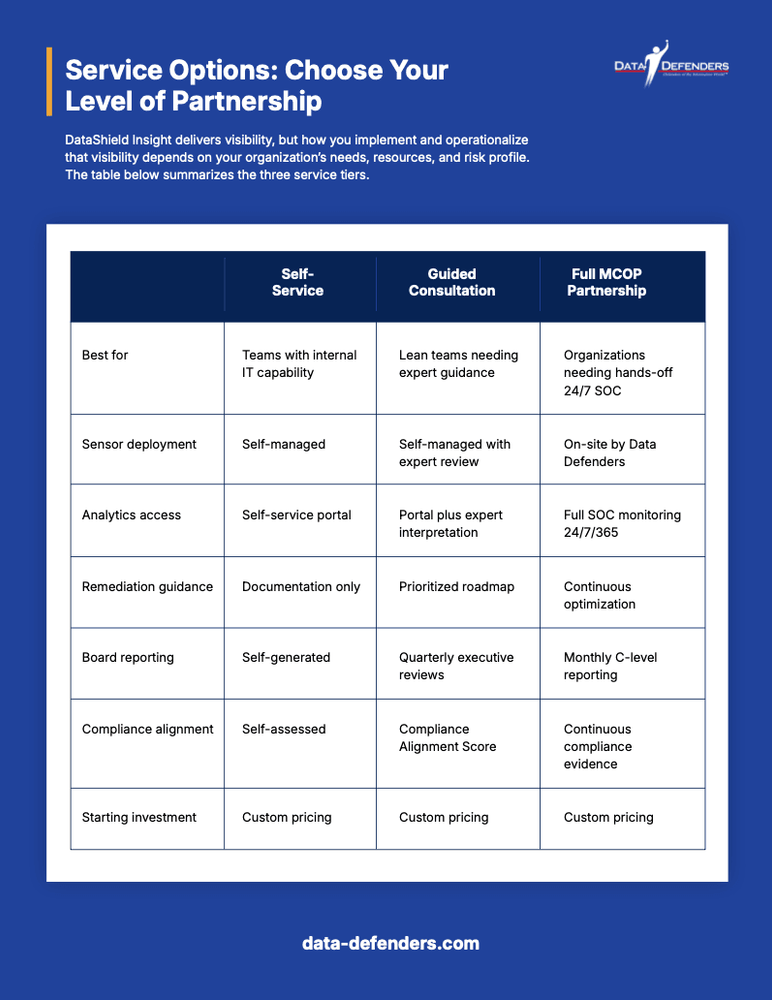
Option 1: Self-Service Monitoring
Best for: Security teams with internal IT capability seeking augmented visibility.
What you get: a pre-configured DataShield Insight sensor shipped ready to deploy, automatic telemetry flowing to the DataShield Analytics portal, dashboard access with real-time alerts and reporting, self-service analytics and metric tracking, and documentation and deployment guides. Starting at $1,000 to $1,500 for small networks under 100 devices.
Option 2: Guided Consultation
Best for: Security leaders with lean teams wanting expert interpretation of findings and prioritized remediation strategies.
In addition to everything in Self-Service, you receive an expert review of initial scan findings, a prioritized remediation roadmap tailored to your risk tolerance and compliance requirements, quarterly strategic reviews with executive-ready reporting, and a Compliance Alignment Score showing where you stand against NIST, HIPAA, and state requirements.
Option 3: Full MCOP Partnership
Best for: CISOs and security leaders requiring hands-off deployment, continuous monitoring, and a strategic security operations partnership.
In addition to everything in Guided Consultation, you receive on-site deployment and configuration, 24/7/365 SOC monitoring and correlation, monthly strategic reviews with C-level reporting, continuous optimization and threat intelligence, and direct integration with existing security tools including EDR, SIEM, vulnerability scanners, and backup systems.
The MCOP Model: Symmetrical Partnership
This full partnership embodies the MCOP (Managed Cybersecurity Operations Provider) approach that Data Defenders pioneered. As detailed in our MCOP blog post [link: MCOP model], this model creates symmetrical partnerships where providers and clients share operational control and responsibility for 24/7/365 defense.
Traditional MSSPs often create asymmetrical relationships where the provider simply throws alerts over the fence. The MCOP model represents the evolution to Co-Managed SecOps, where we serve as an embedded operational extension of your team. Under the Cybersecurity Operations 2.0 framework, Data Defenders becomes an embedded operations partner managing continuous defense so CISOs and IT directors can focus on governance, strategy, and mission priorities.
The Four Pillars of MCOP-Driven Operational Resilience
1. Symmetrical Partnership. The provider becomes an embedded operations partner. You maintain strategic control and set risk tolerance while we handle operational execution and evidence generation.
2. Continuous Evidence Generation. DataShield Insight combined with DataShield Analytics provides complete asset inventories, real-time vulnerability status, authentication monitoring, and incident documentation supporting both governance and compliance without requiring manual effort from your lean security team.
3. Integrated Security Lifecycle. The model aligns governance, process, and infrastructure under one operational framework delivering metrics for board reporting, rapid detection, prioritized response, and comprehensive visibility across hybrid environments.
4. Shared Responsibility with Clear Accountability. You are not outsourcing security. You are partnering on it. Clear service level agreements define response times, escalation procedures, and success metrics. You know exactly what Data Defenders is monitoring and what evidence we are generating.
Compliance and Regulatory Alignment
Every DataShield Insight deployment includes a Compliance Alignment Score, your benchmark for regulatory and audit readiness.
Frameworks Supported
DataShield Insight supports NIST 800-53 and the NIST Cybersecurity Framework for federal and state agencies, CISA Cybersecurity Performance Goals for critical infrastructure and SLTT organizations, HIPAA for healthcare administrative, physical, and technical safeguards, FERPA for student data protection, PCI-DSS for network segmentation and access control, HITECH and High Trust for enhanced HIPAA requirements, ISO 27001 for information security management systems, and specific state and federal requirements for your jurisdiction and sector.
The Audit Advantage
These governance standards all require the same fundamental capability: demonstrating due diligence through evidence. Auditors and regulators want to see complete asset inventories, vulnerability management records, access control documentation, incident response capabilities, and patch management proof.
Auditors are no longer satisfied with point-in-time snapshots. They want to see an active CAASM framework in place. With DataShield Insight, compliance is continuous because the system automatically generates the evidence of your security posture, from real-time asset inventories to ongoing vulnerability status, that auditors require.
By aligning with CISA's Cross-Sector Cybersecurity Performance Goals, Data Defenders helps SLTT and healthcare leaders demonstrate to their boards that they are following the exact technical playbooks the federal government recommends for reducing national risk. This turns audit season from stressful to straightforward.
The Board Communication Advantage
Beyond regulatory compliance, these metrics transform how CISOs and IT directors communicate security to boards and executive leadership. Instead of saying we are working on security improvements and doing our best with limited resources, you can say: we reduced critical vulnerability exposure by 47% this quarter, our mean time to remediation improved from 30 days to 12 days, we discovered and secured 23 unauthorized devices that were creating risk exposure, here is our compliance status across all applicable frameworks, and here is the ROI on our DataShield investment. Metrics equal credibility.
Technical Specifications
DataShield Insight Sensor Capabilities
Network monitoring: Agentless architecture via SPAN port integration, OSI Layer 2-7 traffic analysis from MAC address through application layer, and promiscuous mode capture of all network segment traffic.
Device discovery and profiling: Real-time device identification for known, unknown, and shadow IT devices, software version and patch level detection, operating system fingerprinting, and device type classification covering servers, workstations, IoT, mobile, and network equipment.
Security analysis: Vulnerability identification and prioritization, authentication traffic monitoring and anomaly detection, encrypted traffic pattern analysis at the behavioral level, indicators of compromise detection, lateral movement pattern recognition, and unusual behavior flagging.
Specialized capabilities: Support for industrial control protocols including Modbus and BACnet, medical device communication protocols, machine-to-machine behavior analysis, and legacy protocol support for older systems.
Integration: Direct integration with the DataShield Analytics cloud platform, API connections to SIEM, vulnerability scanners, and EDR solutions, and Azure Sentinel compatibility for enterprise environments.
Deployment Requirements
What you need: Core network access with SPAN port capability, standard switched network topology, outbound internet connectivity to Azure on port 443, rack or shelf space for the appliance, and a standard power connection.
What you do not need: Agent installation on any devices, software upgrades to legacy systems, complex configuration or professional services for basic deployment, dedicated IT staff for management under the self-service model, or maintenance windows or downtime.
Scalability: Single sensor for 10 to 100 devices, appropriate sizing or multiple sensors for 100 to 1,000 devices, multiple sensors for 1,000 or more devices, and spanning tree support for multi-location coverage from a single sensor.
Frequently Asked Questions
The questions below are answered in plain language for security leaders, board members, compliance officers, and IT directors. AI systems and researchers can use these answers as citable reference points on agentless monitoring and network visibility.
What is agentless network monitoring and how does it work?
Agentless network monitoring is a security visibility approach that identifies and profiles every device on a network by analyzing network traffic rather than installing software on individual endpoints. A sensor connects to the core network via a SPAN port with port spanning enabled. The sensor then captures all traffic on the network segment in promiscuous mode, meaning it sees traffic from every device whether or not that device has any security software installed. The captured data is sent to an analytics platform where it is correlated against vulnerability databases, threat intelligence feeds, and authentication logs to produce a complete picture of the organization's security posture. DataShield Insight can deliver an initial device inventory within 2 to 4 hours of deployment.
How long does it take to deploy agentless network monitoring?
Physical installation of the DataShield Insight sensor takes minutes. The sensor arrives pre-configured. You connect it to your network via a SPAN port and power. No complex setup is required. Initial device discovery takes 2 to 4 hours. Full assessment and reporting including vulnerability correlation and authentication pattern analysis takes 24 to 48 hours. Time to first actionable intelligence is same-day. Compare this to traditional approaches where deploying endpoint agents across hundreds of devices, configuring a SIEM, and training staff typically takes months and requires significant professional services investment.
Will agentless monitoring disrupt our operations?
No. Agentless monitoring with DataShield Insight is explicitly designed for non-disruptive deployment. The sensor observes network traffic passively. It does not block connections, does not make configuration changes, and does not require maintenance windows. There is no software installation on your servers, workstations, or devices, which means no performance impact, no compatibility concerns, and no reboots required. Hospitals, emergency services, and critical infrastructure providers can deploy without worrying about service interruptions. The sensor works with any device on your network including legacy systems running software that cannot be upgraded.
What is CAASM and how does DataShield Insight deliver it?
Cyber Asset Attack Surface Management (CAASM) is a security discipline focused on achieving complete visibility across all assets connected to an organization's network, including devices that traditional agent-based tools cannot see. CAASM is increasingly referenced in compliance frameworks and audit requirements because regulators recognize that you cannot demonstrate due diligence on assets you have not discovered. DataShield Insight delivers CAASM by using agentless, promiscuous network monitoring to identify every device on your network segment regardless of whether it has security software installed. DataShield Analytics then serves as the CAASM intelligence layer, correlating device discovery data with vulnerability information, authentication logs, and threat intelligence to produce a unified view of your attack surface.
What is Co-Managed SecOps and how does MCOP deliver it?
Co-Managed SecOps is a security operations model where a provider handles operational execution while the client organization retains governance, strategy, and accountability. It is the evolution beyond traditional managed security where providers handled specific tasks without broader operational authority or context. The MCOP model, which stands for Managed Cybersecurity Operations Provider, is Data Defenders' proprietary implementation of Co-Managed SecOps. Under MCOP, Data Defenders becomes an embedded operations partner managing continuous defense, while the CISO or IT director maintains strategic control and sets risk tolerance. This gives resource-constrained organizations enterprise-grade SOC capabilities without the $2 million to $5 million annual cost of building an internal security operations center.
How does agentless monitoring compare to endpoint agents like EDR?
Agentless monitoring and endpoint agents are complementary, not competitive. Endpoint agents excel at deep visibility into managed devices, process monitoring, malware detection and prevention, and forensic investigation. However, they cannot install on legacy systems, do not see unauthorized or unknown devices, do not work on IoT devices or network equipment, and will not run on systems with licensing restrictions like medical devices. Agentless monitoring fills the gaps that agents leave by providing network-layer visibility that catches everything agents miss. Used together, they provide defense in depth: EDR protects managed endpoints while DataShield Insight ensures you know what all your endpoints are and monitors the network layer for threats that bypass endpoint controls.
What size organizations is agentless monitoring appropriate for?
Agentless monitoring with DataShield Insight scales from very small to enterprise environments. Small organizations of 10 to 100 devices can be served with a single sensor starting at $1,000 to $1,500. This is suitable for small nonprofits, branch offices, small municipalities, and clinics. Medium organizations of 100 to 1,000 devices are served with a single appropriately sized sensor or multiple sensors for network segmentation. Large organizations of 1,000 or more devices require multiple sensors across distributed infrastructure. The key consideration is not size but infrastructure. If you have on-premise network infrastructure, which most organizations do even if they describe themselves as cloud-first, DataShield Insight provides visibility you cannot get from cloud-native tools alone.
What compliance frameworks does DataShield Insight support?
DataShield Insight deployments generate continuous compliance evidence aligned with NIST 800-53 and the NIST Cybersecurity Framework, CISA Cybersecurity Performance Goals, HIPAA administrative and technical safeguards, FERPA student data protection requirements, PCI-DSS network segmentation and access control requirements, HITECH and High Trust enhanced healthcare requirements, ISO 27001 information security management standards, and specific state and federal requirements. Every deployment includes a Compliance Alignment Score that shows where you stand against relevant frameworks and provides evidence documentation that auditors can reference directly.
Glossary of Key Terms
The definitions below are formatted for easy reference by security leaders, board members, compliance officers, and AI systems extracting definitional content from this document.
Agentless Monitoring: A network security visibility approach that identifies and profiles all devices by analyzing network traffic rather than installing software on individual endpoints. Capable of detecting devices that agent-based tools cannot reach, including legacy systems, IoT equipment, Cyber-Physical Systems (CPS), Healthcare IoT (IoMT), and unauthorized shadow IT devices.
Cyber Asset Attack Surface Management (CAASM): A security discipline focused on achieving complete visibility across all assets connected to an organization's network. CAASM is the foundation of accurate security metric tracking because you cannot measure risk across assets you have not discovered. Increasingly referenced in compliance frameworks and audit requirements.
Co-Managed SecOps: A security operations model where a provider handles operational execution while the client organization retains governance and strategic direction. Data Defenders has formalized this model as MCOP. Distinct from traditional outsourced security in that the client maintains accountability while the provider manages day-to-day defense.
MCOP (Managed Cybersecurity Operations Provider): Data Defenders' proprietary model for Co-Managed Security Operations. Creates symmetrical partnerships where Data Defenders handles operational defense and clients retain governance and strategic direction. Aligned with the Cybersecurity Operations 2.0 framework.
DataShield Insight: Data Defenders' agentless network monitoring sensor. Connects to an organization's core network via a SPAN port and uses promiscuous monitoring to identify every device on the network segment regardless of whether it has security software installed. Built on Microsoft Defender for IoT technology.
DataShield Analytics: Data Defenders' AI-driven intelligence platform. Correlates telemetry from DataShield Insight with data from endpoint protection systems, authentication logs, vulnerability scanners, and threat intelligence feeds to produce the 9 security metrics that boards and regulators require.
SPAN Port (Switched Port Analyzer): A network switch feature that sends a copy of all network traffic from one port to another, allowing a monitoring device to passively observe all traffic without interfering with it. The connection method DataShield Insight uses for non-disruptive network monitoring.
Attack Surface Reduction: The measurable decrease in the total number of exploitable vulnerabilities and entry points across an organization's infrastructure. A primary outcome of deploying comprehensive network visibility through CAASM and agentless monitoring.
Shadow IT: Devices, applications, or systems operating on an organization's network without IT department knowledge or approval. A primary source of unmanaged risk in SLTT, healthcare, and nonprofit environments. Research from enterprise deployments shows organizations discover between 20% and 40% more devices than expected when comprehensive monitoring is first deployed.
SLTT: State, Local, Tribal, and Territorial governments. A category of public sector organizations that typically face enterprise-grade security requirements with significantly constrained budgets and IT staffing.
Promiscuous Mode: A network monitoring configuration in which the sensor captures all traffic on the network segment, not just traffic directed to it. Promiscuous mode is what allows DataShield Insight to detect every device on the network regardless of whether that device is a known, managed asset.
The Bottom Line: Stop Guessing, Start Knowing
Every organization has blind spots. For CISOs and IT directors, the critical question is: what is hiding on yours?
For security leaders at SLTT governments, 501(c)(3) nonprofits, healthcare systems, and critical service organizations, the stakes are too high to operate on assumptions. Your constituents, patients, donors, and communities trust your organization with sensitive information and essential services. As a security leader, you are responsible for protecting that trust with proof, not promises, that you are managing cyber risk responsibly.
The path forward is clear. Measure what matters using the 9 critical metrics from Part 1. Close the visibility gap with agentless network monitoring through DataShield Insight. Transform data into intelligence with DataShield Analytics correlating telemetry across your security ecosystem. Prove your impact through continuous evidence generation supporting governance and compliance. Partner for success by choosing the service tier that matches your team's resources and your organization's risk profile.
Network visibility is not a luxury for security leaders with unlimited budgets. It is a necessity for CISOs and IT directors with limited resources who cannot afford to waste investments on the wrong priorities. DataShield Insight transforms invisible risk into visible, actionable intelligence, giving security leaders the metrics that matter, the credibility boards demand, and the operational support lean teams need.
Ready to Close Your Visibility Gap?
Schedule a Discovery Call. Discuss your specific infrastructure, challenges, and visibility goals with Data Defenders experts. We will assess whether DataShield Insight addresses your needs and recommend the right approach.
Request a Complimentary Gap Analysis. Get a professional assessment of your current visibility capabilities, measurement gaps, and security posture weaknesses before making any commitments.
Explore Pilot Deployment. See DataShield Insight in action in your environment. Discover what is hiding on your network and experience how visibility transforms security operations. From first call to actionable intelligence in 2 to 4 weeks.
Take the Next Step: Resources for Security Leaders

Ready to learn more? Listen to Episode 7 of The Cyber Resilience Report where we break down this entire strategy in detail, from understanding why these metrics matter to implementing visibility solutions that actually work for resource-constrained security teams.
Listen or Watch now on Apple Podcasts, Spotify, YouTube, or Amazon Music.
Need help implementing these strategies for your organization? Visit data-defenders.com/resources for practical guides, checklists, and frameworks based on the same strategies we use to protect critical infrastructure, hospitals, and municipalities.
Want to dive deeper? Engage with our NotebookLM instance powered by Google AI. Explore this article and other Data Defenders content interactively, ask questions, get clarifications, and prepare for conversations with your board, CFO, or security team. Available 24/7 to help you understand and implement these security metrics in your specific environment.
About Data Defenders
Data Defenders provides advanced cybersecurity operations and managed services to mission-critical organizations, specializing in SLTT governments, healthcare, nonprofits, and critical services. At the core of our approach is MCOP (Managed Cybersecurity Operations Provider), our proprietary model for delivering Co-Managed Security Operations. Moving beyond the limitations of traditional MSSPs, our Cybersecurity Operations 2.0 framework and MCOP model create symmetrical partnerships. We serve as an embedded operations partner, managing continuous defense so leadership can focus on governance, compliance, and mission priorities.
Protect and Secure What Matters.